A hosting service provider from South Korea recently paid about $ 1 million in cryptocurrency to the developers of a cryptographer program. Why so much? The fact is that ransomware infected 153 servers running on Linux. These servers host 3,400 customer site sites.
Initially, the developers of the malware wanted to get about $ 4.4 million. The company said that it was too much and was not able to pay that amount. After that, the cybercriminals agreed to moderate their appetites, satisfied with “only” $ 1 million. Now, the company's employees are engaged in data recovery. This is not such a fast process, so customers will have to wait until all their sites and services start working again.
"This is a difficult task, but I am doing everything that depends on me, and I will do everything to restore the servers to work,"
said a company representative.
It is worth noting that the main problem with this malicious software is that it works with Linux. Ramsomware was named Erebus (previously there was a version of this malware attacking Windows systems). How the virus penetrated the company's servers is not yet clear. Technical support is sorted out, trying to understand what has happened.
Third-party experts, who also studied the situation,
argue that the problem may be in outdated software that was used by the hoster. For example, the site Nayana worked on a server with Linux with a kernel version 2.6.24.2 (2008). This version has many vulnerabilities, including Dirty Cow, which allows attackers to gain root access to the system. In addition to the outdated version of the kernel, the company worked with Apache version 1.3.36 and PHP version 5.1.4, all of which were released back in 2006. It would be superfluous to say that over the past ten years, attackers have studied this software far and wide, learning how to crack everything they need.
Erebus first
appeared in September 2016 (or rather, was first discovered). Then came its updated version, it happened in February 2017. Then the developers "taught" their product to bypass the User Account Control in Windows.
Interestingly, now the Linux-version of Erebus operates mainly in South Korea. Maybe because not only Nayana uses outdated software, but other hosting companies in this region are doing the same.
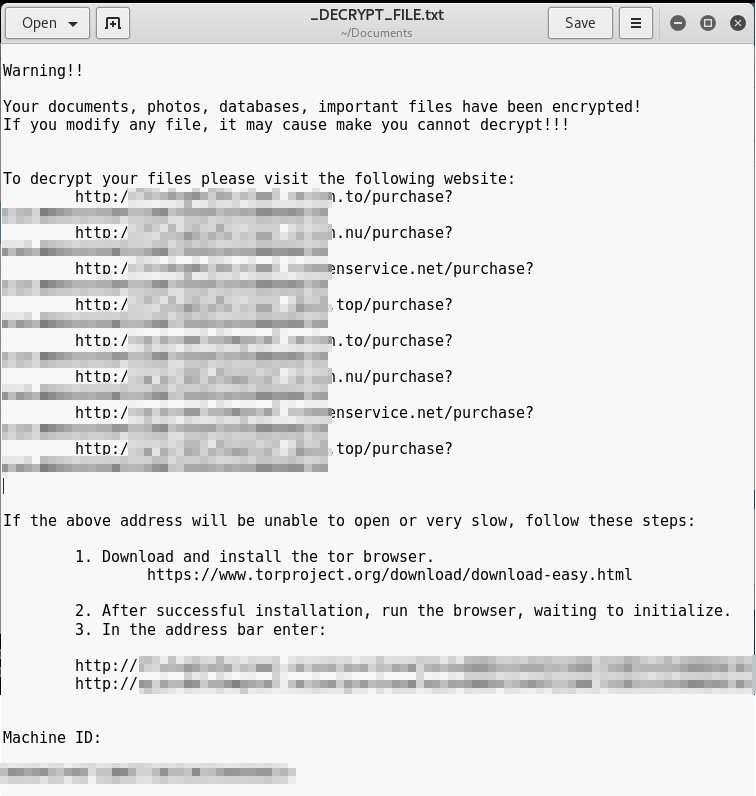
| Header (0x438 bytes) |
| RSA-2048-encrypted original filename |
| RSA-2048-encrypted AES key |
| RSA-2048-encrypted RC4 key |
| RC4-encrypted data |
This can be done only with the key that you need to buy from the attackers. The fact is that first the files are encrypted using RC4 block by block, with a block size of 500 KB. The keys for each block are generated randomly. Then the RC4 key is already encoded, this is done using the AES algorithm, which is saved in the file. And this key is already encrypted by the RSA-2048 algorithm, which is also stored in the file. These keys are generated locally and are available. But these are public keys, but private keys are encrypted using AES and another randomly generated key.
The Erebus version in question encrypts 433 different file types. As mentioned above, you can’t get a private key by any other method except to redeem it from an intruder. This was verified by several experts who conducted an analysis of the attack.
Now the hoster is working closely with law enforcement agencies in South Korea in order to try to detect intruders. But, of course, besides searching for a company, you should first restore the servers and customer data, then update outdated software, and only then direct all your efforts to work on finding intruders.
Hoster from South Korea is not the only organization who had to pay the attackers. Last year, the key to decrypting files was
bought by a school from the USA, on whose servers a successful attack was carried out. True, in this case it was not about a million US dollars, but about $ 8500.
And in November last year, because of the cryptographer,
all passengers on the narrow-gauge railway of San Francisco were able to ride for free. The fact is that the cryptographer encrypted all payment terminals of the transport company San Francisco Municipal Transportation Agency (
SFMTA ).
Last year, she paid ransomware and hospital developers, whose servers were also infected with malicious software. At the moment, the record holder for payments, as far as can be judged, is the company Nayana, which was discussed above. Perhaps someone paid more, but nothing is known about these cases, most likely the victims just want to remain anonymous.