
Developers of the smart weapon from which only its owner can shoot, promise an unattainable (so far) ideal. If a phone or computer can be blocked until a person confirms his identity, then why not apply a similar principle to a firearm? The hacker under the pseudonym Plore studied the security mechanisms of one of the manufacturers of weapons with authentication and found that if smart guns are common everywhere, they should be even smarter.
Plore
found a number of critical vulnerabilities in the smart gun of the German manufacturer Armatix IP1 and was able to crack it with several tricks. The gun is designed in such a way that it can only be activated if the owner wears a special Armatix watch. If the watch "does not see" the gun and cannot communicate with it using a short radio signal, then the weapon will not work. So at least, says Armatix. However, Plore has demonstrated that he can expand the range of the clock’s radio signal, allowing anyone to shoot a pistol if he is more than three meters away.
The hacker also found out that you can kill the gun’s radio signal so as not to allow the owner to shoot, even if the watch is a few centimeters and connected to the weapon. Moreover, it is possible to mechanically disable the shutter mechanism of the pistol by placing several cheap magnets near its barrel, so that it can shoot at all without a watch.

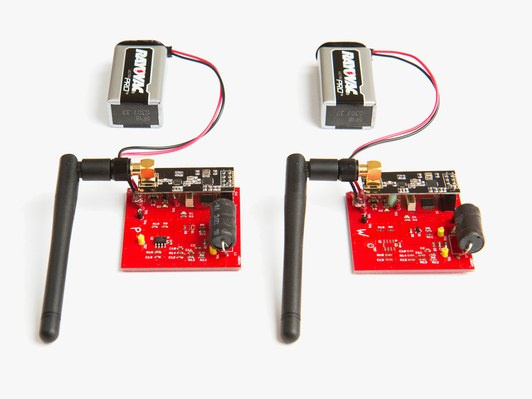
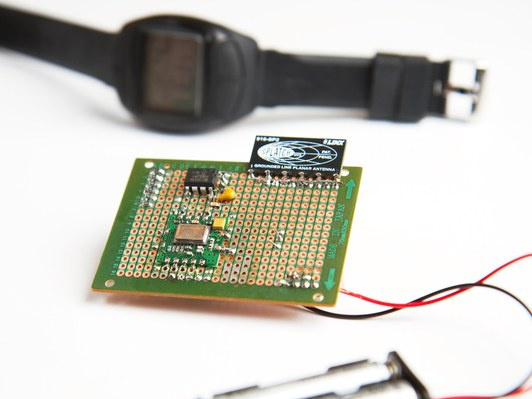
Plore has been developing a series of attacks on IP1 security mechanisms for about six months. “I was sure that I could break this weapon, but I didn’t think it would be so easy,” he notes. The hacker himself works as a hardware engineer and security consultant. Before coming to a solution with magnets, Plore tried a more technical approach of a relay attack. He created two small radio grads, each the size of a deck of cards, spending only $ 20 on them.
When the shooter squeezes the pistol's handle, the weapon sends an RFID signal to check if there is a clock on the arm. If you put one of the devices developed by a hacker near the clock, you can intercept the signal and transmit it to a second device up to 3.5 meters away. This means that another person can “intercept” the gun and apply it to the owner or to anyone else.
The hacker also developed a technique that does not bypass the authentication system, but violates the security mechanisms, making the weapon completely useless. This is possible with the help of a transmitter for the same $ 20, which simply radiates radio waves at about the same frequency (900 MHz) as the gun and the clock, suppressing their connection. Such a portable transmitter can disrupt the operation of the gun from a distance of 3 to 4.5 meters. An attacker who knows his victim is carrying an Armatix pistol can use the transmitter to disarm her. However, the hacker warns that interference with the pistol and watch can cause a normal smartphone.
After developing radio receivers, Plore found Armatix patent schemes and found out that when the radio signal from the clock allows the gun to fire, the radio magnet moves a small metal plug to unlock the
drummer - the core that breaks the cap. The hacker bought a set of magnets for $ 15 and put them near the barrel of a pistol at a certain angle, and the weapon fired by pressing the trigger hook without any hours. “When the gun first fired without authentication, I could not believe that it worked. I tried to shoot again, and I succeeded. So I learned how, for $ 15, you can beat the security system of a smart weapon worth $ 1.5 thousand, ”recalls Plore.
Having arrived at this conclusion, the hacker contacted Armatix in April 2017, but the company did not react to the results of the experiment at all — it only recognized that it had received them. Later, Armatix spokesman Georg Jahnen expanded the company's message and noted that although all attacks presented by the hacker are possible, they are difficult to implement in field conditions. The attack with the suppression of the connection between the pistol and the clock actually demonstrates the safety of the weapon - the pistol simply stopped working and did not start shooting.
As for the attack with the magnets, Jahnen is sure that an attacker who wants to exploit this vulnerability at an unexpected moment may not have magnets ready for use. However, at the same time, a company spokesman admitted that the Plore IP1 error message in the future will make smart guns safer.
There is no software patch for IP1 that can fix the vulnerability. But future models of weapons from other manufacturers may combine a pistol and a controlled device in conjunction with more stringent restrictions on signal transfer time. Error correction and more powerful radio signals can also be used to prevent interference. Finally, to prevent a magnet attack, you can create your own non-ferrous metal blocking mechanism.