
Miners cryptocurrency on websites have become a real problem. Recently, even
The Pirate Bay began testing this monetization option. The first services appeared like Coinhive, which agitate site owners to install miners and earn money without banners and advertisements. According to
their calculations , an ordinary site visitor on an average laptop generates 30 hashes per second. For
The Pirate Bay, with an average session time of 5 minutes and a monthly audience of 315 million people, this gives 30 × 300 × 315000000 = 2,835,000 mega-mixes per month.
If you treat people humanely and load the processor only at 30%, then there are 850,000 megaheshes. Coinhive pays $ 0.00015 XMR for one million hashes to website owners, so
The Pirate Bay could earn 127.5 XMR ($ 12,000) per month and completely kill its reputation in the eyes of users.
Unfortunately, more and more sites are choosing this option of monetization. Sometimes miner scripts penetrate sites without the knowledge of the owners themselves. One such story was recently
told by one of the users of Habr . He accidentally discovered a miner on a small Russian website selling pet products.
Worse, the attackers began to deploy hidden miners directly into browser extensions, so that they can work continuously, stealing computing resources. For example, a few days through the official Chrome Web Store
, the SafeBrowse extension with the miner was distributed before it was deleted. For Firefox came out
two extensions with miners .
Naturally, we are not happy with this prospect. From the point of view of an ordinary person, the main problem is how to protect oneself from these miners so that they do not overload the processor, do not brake the computer, and do not devour electricity.
Users of the uBlock Origin ad blocker have been
discussing a problem on GitHub for several weeks and are listing malicious domains to block. Unfortunately, recently miner scripts started to randomly change domains, so it’s not easy to block scripts, unless you disable the implementation of JavaScript in the browser at all.
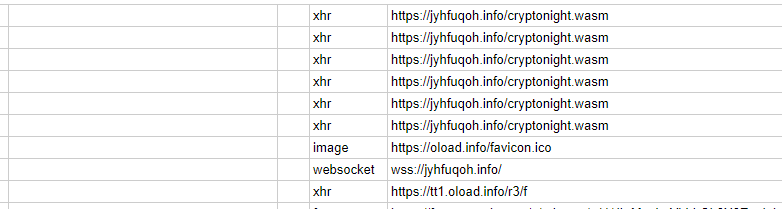 A miner script that uses random domains is difficult to block with standard blockers.
A miner script that uses random domains is difficult to block with standard blockers.However, scripts with random domains are rarely found. You can protect against most miner scripts by blocking at least the most popular domains in hosts - and keeping the list up to date by adding new domains there as they are discovered. Recently, a free Anti-WebMiner program has appeared that does just that: its authors
add to the list of miner domains on GitHub, and the program itself adds these domains to the hosts file.
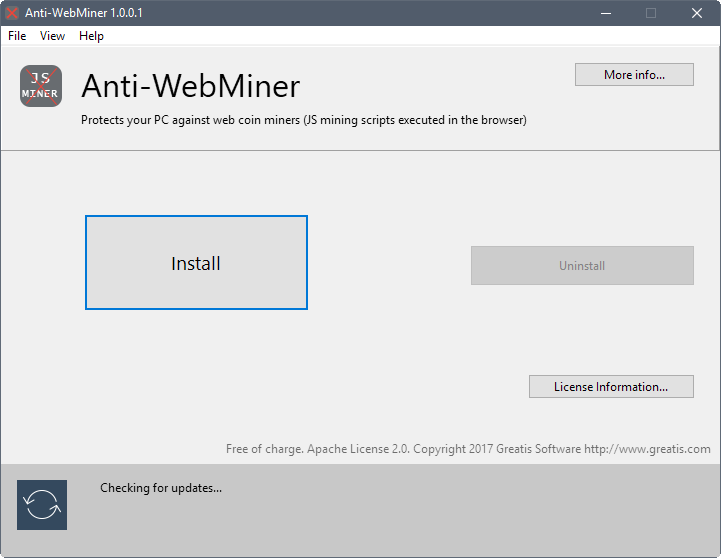
This can be done manually. At the moment, the list includes 16 domains, including the domain of the aforementioned Coinhive, although it positions itself as a legal service for website owners:
# Anti-WebMiner Start 1.0 43011
0.0.0.0 azvjudwr.info
0.0.0.0 cnhv.co
0.0.0.0 coin-hive.com
0.0.0.0 gus.host
0.0.0.0 jroqvbvw.info
0.0.0.0 jsecoin.com
0.0.0.0 jyhfuqoh.info
0.0.0.0 kdowqlpt.info
0.0.0.0 listat.biz
0.0.0.0 lmodr.biz
0.0.0.0 mataharirama.xyz
0.0.0.0 minecrunch.co
0.0.0.0 minemytraffic.com
0.0.0.0 miner.pr0gramm.com
0.0.0.0 reasedoper.pw
0.0.0.0 xbasfbno.info
# Anti-WebMiner EndAlthough no one bothers to edit the hosts manually, but with this utility it is faster and more convenient to update the list of domains and make changes to the hosts.
The list of "prohibited" domains can also be manually entered into the ad blocker program you use.
There are other options for blocking miner scripts. For example, the extension
No Coin for Chrome (
source code on GitHub ).
The No Coin extension discovered a minerskite on the siteThis extension monitors the activity on each site - and signals if a miner script is found on it. This approach even helps against scripts with random domains. In addition, here you can put the site on the white list, if you really want to donate part of the CPU time to it. For example, many users of
The Pirate Bay in the comments to the news about testing a mining script expressed the opinion that they are not against helping their favorite site with their CPU time. Over the past year, this torrent tracker has collected only $ 3,500 donations, and through a miner script can collect $ 12,000 a month, while people do not have to part with money (at least, not directly). People are pumping wares, free music and movies, so why not give something in return.
The other
minerBlock extension for Chrome works on the same principle as No Coin. It also spreads with open source, so you don’t have to worry that the miner blocker quietly mines cryptocurrency.
Still, the most reliable way to block miner scripts is to install an extension that generally blocks the execution of any scripts, like
NoScript for Firefox.