There is not a lot of RAM: any available volume is sufficient only “for the time being, until time”, and there exists where to apply it. Well, when it is really useful tasks. Job. Games. Research. It's bad when the RAM ends not through the fault of the user, but because of the developer.

There are many reasons for this, the ways to solve it ... let's take everything in order.
Return my 97th
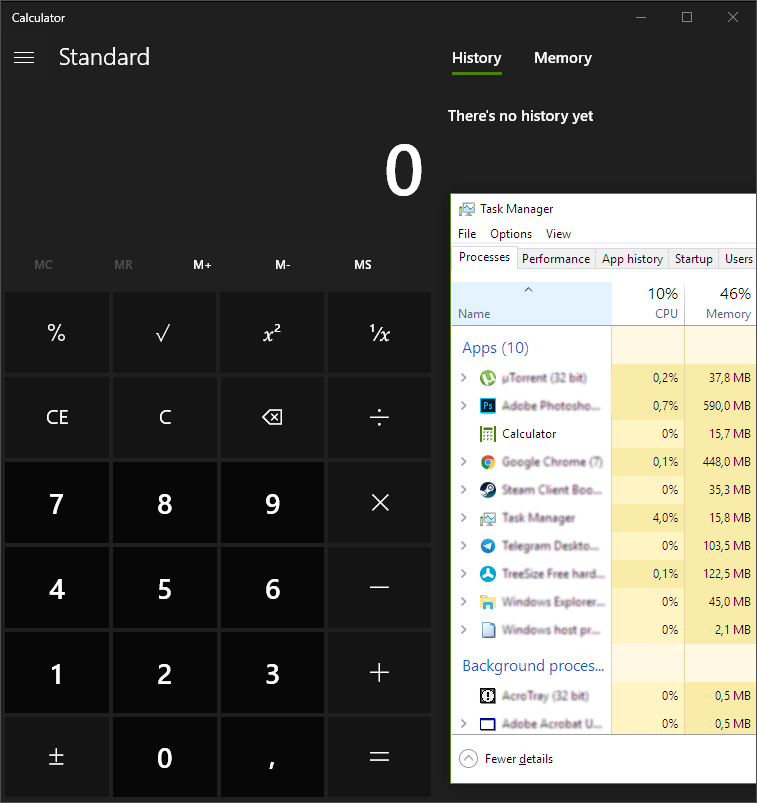
Illegal seizure of RAM by applications is a direct consequence of technological progress. Computational resources, thanks to Moore's law, become more (and their price falls from year to year), and the cost of the work of a highly qualified specialist, alas (and again, fortunately for us, IT's), follows the reverse trend. Applications are overgrown with new features, the next layers of abstractions are introduced for rapid development ... Twenty years ago the code was much closer to the hardware than it is now. A huge number of layers and intermediate technologies - one of the many evils, leading to a deplorable situation. 15 megabytes of RAM for (!) Calculator. Nightmare!
And it would be okay if the situation improved, so no: the developers take the old tools, come up with even simpler and more functional new ones, it takes several years and the cycle repeats. Just think, recently we rejoiced at CSS 3.0 and rounded corners with a simple property of an object, then Bootstrap, now - another superstructure-combine. Write less, do more to all fields.
Comfortable bread trolley
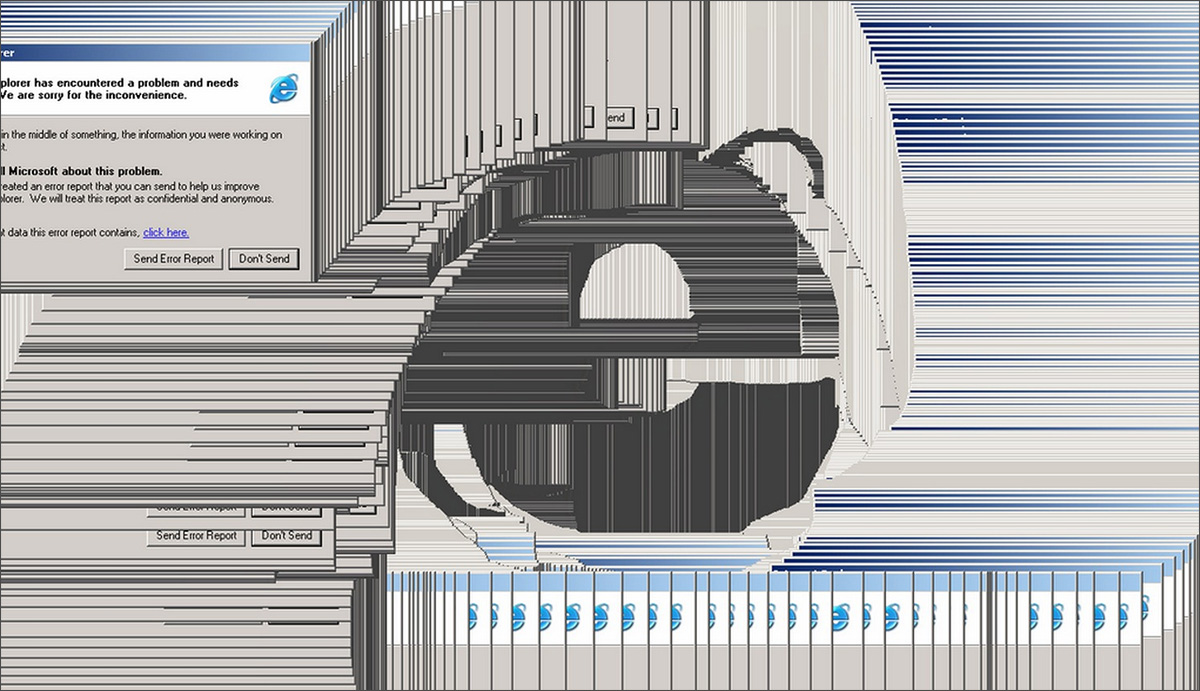
Modern browsers are not only valuable hypertext, but also three or four dozen useful features. Video playback, work with documents, and other extensions are almost an operating system in miniature. With a bunch of own modules from different developers, and all this is connected somehow. It often works the same way. Million open tabs, complex layout, the framework on the framework is one of the main leak generators.
How to fight? To install some kind of ad blocker and extension such as The Great Suspender, which unloads unused pages from memory and saves them in the “minimum” tab - it is convenient and effective to reduce background memory loss.
Not all adblock's are equally useful.
Yes, software that cuts out annoying banners and the code of all kinds of trackers, in certain cases, reduces the load on the processor and on the RAM. But not always. The effectiveness of this solution depends directly on the quality of its execution. Software that works at the system level as a proxy server (cuts off traffic from advertising sites before it enters the browser) by itself consumes a certain amount of memory, but it is more or less static. But extensions and modules for popular browsers create monstrous constructions in place of the cut out advertising frames. Yes, advertising on the page becomes less, only memory consumption by this tab can grow not by some 10-15%, but
several times .
Resource Caching Issues
This mostly affects sandbox games, both stationary and launched inside the browser: Factorio, Rim World, Minecraft with lots of mods ... Under certain circumstances (for example, they left the production for the night so that the game earned while you sleep) you can wake up with tightly hanging computer. Well, or very slowly working. At the same time, in terms of RAM, everything will be “OK” - as much as the game consumed, it consumes as much.
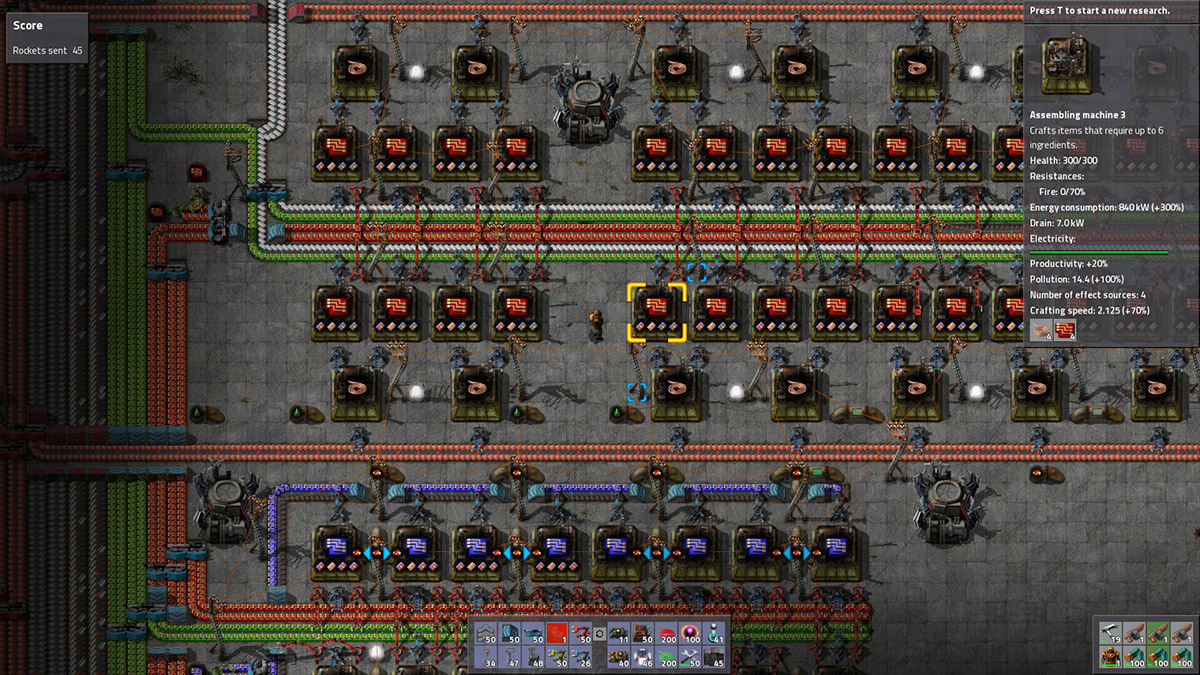
In 90% of cases of this behavior, users have an SSD installed and both the paging file and the hibernation mode are enabled. The game dumps unused resources from the RAM into a swap, “Winda” caches them and saves them in case of going to sleep, then the graphics are reused and re-deposited in the “long box”. But the old copies are not deleted anywhere - after a few hours, depending on the capacity of the drive, the free space on it ends, the system drops before reloading and clearing temporary files. If the game did not try to “optimize” the expenditure of RAM, unloading and re-pumping up resources, it would flow as usual, with a gradual slowdown and subsequent crash.
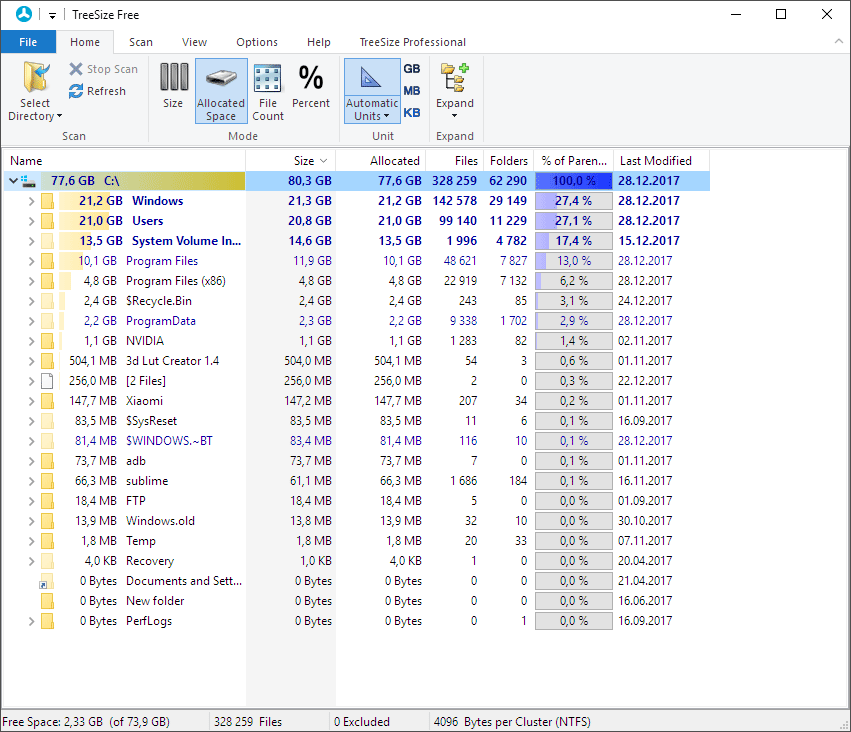
Solution options: testing a hypothesis with a utility like TreeSize, deleting accumulated junk assets, transferring paging to a solid HDD or disabling hibernation in Windows 10, writing a bug report to the forum, waiting for a patch.
The developer paws
Sometimes leaks are just leaks. Photoshop loves and can otzhirat large amounts of memory, especially immediately after the release of a new license release. Fortunately, the application itself has a tool for limiting the amount of RAM available (you should not allocate more than 66%), assignment of caching disks and all that. Alternatively, you can wait six months and wait for a stable version. Killerphic are rarely needed to put up with bugs.

Torrent clients. Multiple simultaneous connections, the same amount of simultaneously downloaded files, connection problems - and the corresponding memory consumption. The solution is a limit on the number of outgoing connections and the rate of return. The correct coefficients are selected manually.
Software printers / scanners / cameras. History - food written Hindu code: a curve like a kamasutra. Medicine in this case is powerless - here for the use of open / universal counterparts, or to write bug reports and pray to Shiva to punish the damned hacks.
Miner malvar. Sometimes a memory leak "to nowhere" is a reason to uncover the antivirus. The main protection of cryptocurrency from the "optimization" of their extraction by the hardware method is an increase in the complexity of the algorithm in the direction "more memory is needed for calculations". Therefore, background minniki can burn on the consumption of RAM. Moreover, one can join the number of “miners” unnoticed: what costs only the well-known scandal with
uTorrent , the “bonus” to which users received the miner application Epic Scale. Yes, and one popular
tracker last fall lit up in the background cryptocurrency mining right in the browsers of visitors.
War without end
It will take a lot of time before a high-quality AI is written, capable of raking up the rubble of a curved code. For now it is necessary to struggle with memory leaks by the checked methods: with a tambourine, a whip and a bug report. Or increase the volume and overlook these very leaks. Of course, having 16, 32 or even 64 gigabytes of fast RAM on board is good, and
Kingston will always have the right solution . It is important to remember that any volume is not a hindrance to curved software - it’s just that it’s going to work for a longer time without problems.
Any interesting examples of memory leaks in the system? Write in the comments - everyone will be interested.