
Biometric protection in smartphones and laptops allows you to unlock the device in tenths of a second or quickly launch the application. Fingerprint scanner today is in a variety of smartphones, tablets and laptops.
Paradox, but the more sophisticated passwords become, the more difficult it is to protect the data - ordinary users find it difficult to invent and remember passwords, which every year make them more difficult to do. A biometric authorization eliminates the many inconveniences associated with the use of complex passwords.
Identification technology based on fingerprint, face shape and other unique physiological data of a person has been known for decades, but does not stand still, but is constantly evolving. Today, biometric technology is better than it was ten years ago, and progress does not stand still. But will there be enough "margin of safety" for ordinary biometrics or will it be replaced by exotic multifactor authentication methods?
The origins of biometrics
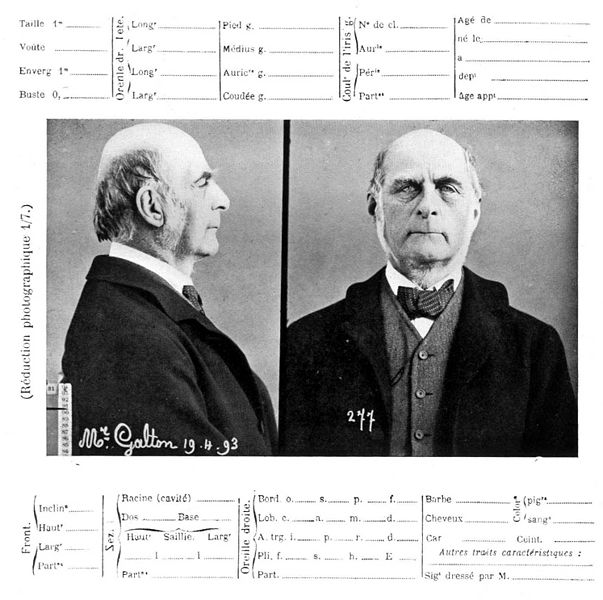
The history of modern identification methods begins in the 1800s, when the clerk of the First Bureau of the Police Prefecture of Paris, Alfonso Bertillon, proposed a method for establishing the identity of criminals. Bertillon developed a systematic approach, measuring several characteristics of the body: height, length and volume of the head, length of hands, fingers, etc. In addition, he noted the color of his eyes, scars and injuries.
Bertillon’s identification system was flawed, but helped uncover several crimes. And later formed the basis for a much more reliable fingerprinting.
In 1877, a British judge in India, William Herschel, put forward a hypothesis about the uniqueness of human skin papillary pattern. Francis Galton, a cousin of Charles Darwin, developed a method for the classification of fingerprints. Already in 1902, the technology of identifying a person by fingerprints was used in the investigation of criminal offenses.
However, even in ancient Mesopotamia, people
used handprints on clay tablets for identification.
The technology that allows us to quickly unlock a smartphone today originates in the 1960s, when computers learned how to scan a fingerprint. At the same time, the face identification technology was developed, where the first major breakthrough occurred in 1968:
when identifying faces for 2000 photos, the computer was able to correctly “identify” more test samples than people.

The first proposed method of data collection using technology is optical. Finger typos are a collection of bumps and cavities that create a specific pattern, a papillary pattern unique to each person. Therefore, it is sufficient to simply photograph and compare with those stored in the database.
Later, the capacitive scanning method was invented: microcondensers determine the pattern on the finger. The method is based on the charge and discharge of capacitors depending on the distance to the skin at each individual point of the field - if the capacitor is located under the tubercle, it sends one type of signal, and if under the hollow, then another.
Signals are combined and compared with encrypted fingerprint information stored on the device.
There are other methods of data collection: they are based on the work of radio frequency scanners, thermal scanners, pressure-sensitive scanners, ultrasound scanners, and so on. Each method has its advantages and disadvantages, but semiconductor capacitive scanners, simple and reliable, are massively distributed in mobile devices.
Finding a strong password
Digital biometric databases have been used in the United States since the 1980s, but it was not until the 1990s that it was possible to begin introducing biometrics into devices designed for ordinary users. At first, biometrics did not attract much interest, since it remained expensive, inconvenient and incomprehensible to the end user. The first scanner built into the laptop read the fingerprint for
about 1 minute .
Gradually, the cost of introducing biometrics decreased, and security requirements grew. Users used the same passwords for everything and did not change them for years. The equipment manufacturers were able to offer them a universal solution - the same one password for everything that does not need to be changed and which cannot be stolen from the user's computer, picked up by brute force or peeped over the shoulder.
In 1994, John Daugman
developed and patented the first iris-based computer identification algorithms. Although the algorithms and technologies have greatly improved since then, it is Daugman's algorithms that are still the basis for all the popular variations of this method. Today, scanning the iris, its retina, and DNA analysis for reliability surpass the fingerprint, but require more complex and expensive technical solutions.
By the 2000s, another biometric technology began to develop - face recognition in real time. The technology is in many ways similar to fingerprint analysis: the characteristic features of the face are compared with the sample stored in the database. On the face is determined by the distance between important points, and also collects detailed information about the form: for example, takes into account the contour of the nostrils, eyes and even skin texture.
Fingerprint vulnerability

As
shown by researchers at Michigan State University, the first mass print scanners can be fooled using a regular inkjet printer and special paper. The researchers scanned the skin on several fingers and simply printed them in 2D with conductive ink on
special paper , which is usually used for printing electronic circuits. The process is very fast. This was not the first attempt to find vulnerability in biometric protection, but earlier it took at least 30 minutes to create a quality sample.
If you invented and remembered a complex password, then no one will “catch” it from your head. And in the case of biometrics, it is enough to find a high-quality imprint of your finger. Experts
have shown that you can take a fingerprint with the help of a marmalade bear if you attach it to the surface of a smartphone. Also, the print can be reproduced by photo or using an application that simulates the unlock screen.
People leave their fingerprints everywhere, as if they were recording their passwords on all the objects and surfaces encountered. But at least you can change the password, and if the biometric material is compromised, then you can not change your eye or finger.
In addition, databases are being cracked all the time. This is less true for smartphones that store information in encrypted form. But government agencies have a lot of biometric information, and these are not the most reliable custodians.
The future of biometric security
Password no one should know no one except you. In the ideal case, you don't tell anyone, write down anywhere, leave no loopholes (the answer to the “secret question” is your dog's nickname) to rule out the possibility of a simple hack. Of course, with the proper desire, you can hack a lot, but in other ways. For example, through the vulnerability in the ancient
SS7 protocol, SMS is intercepted and bypass two-factor authentication - in this respect, biometrics is even more reliable. True, you must be a very important person so that someone spends enough money and effort to break into your smartphone or laptop using all available methods.
The obvious problem of biometrics is its publicity. Everyone knows that you have fingers, eyes and a face. However, “open biometric data” is just the tip of the iceberg. Experiments are underway with all possible characteristic signs, from monitoring your heart rate (this solution is already
being tested by MasterCard ) to implanting chips under the skin, scanning the pattern of intraocular vessels, the shape of ear lobes, etc.
Google’s Abicus project plans to
track the unique features of human speech, which will allow you to authenticate your identity in the future, even while on the phone.
Experimental surveillance cameras track people literally
by their gait - this technology is hard to imagine as a smartphone protection, but it works well in a single smart home ecosystem.
TeleSign has
launched a behavior identifier based on the user's Internet surfing. The application records how the user moves the mouse, in which places the screen most often clicks. As a result, the program creates a unique digital fingerprint of user behavior.
The veins in the wrists, palms and fingers can also be used as unique identifiers - moreover, they
can complement existing fingerprint identification methods. And it is much easier than using an
electroencephalogram instead of a password, which is removed by electrodes on the head.
Probably the future of biometric security is simplicity. Improving modern methods is the easiest way to ensure a massive acceptable level of protection. For example, you can scan an imprint with a 3D projection of all the tiny details, and also take into account the design of the vessels.
Biometric identification technologies are improving so quickly that it is difficult to predict how they will look in a few years. One thing can be assumed rather confidently - passwords that were hard to use, change and remember will remain in the past.