The article will briefly look at how to protect a program using the VK API from illegal use and
unauthorized distribution without creating your own cloud server.
Graphic scheme
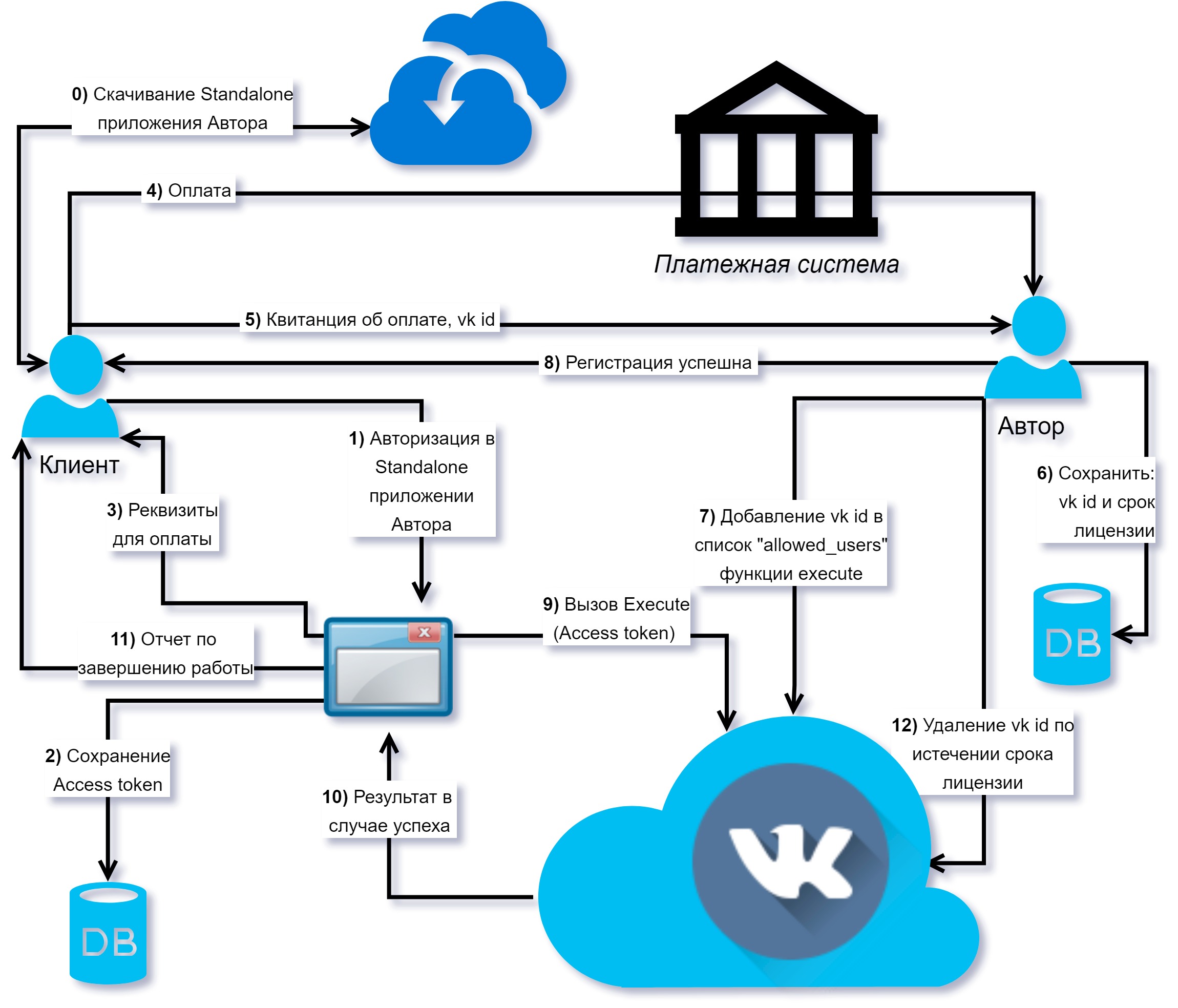
Principle of operation
If the software is not related to Vkontakte, then major developers use
HASP , however, it is expensive, difficult to acquire, and more applications need to be developed that will be launched inside the HASP keys.
This article is about the protection of programs developed by individual developers or small companies. It is logical to place your server on the Internet and use it to license the program, but even this does not guarantee that it is enough to patch the program. Consider how many do this simply by placing critical or complex requests in the form of stored procedures, the code of which is securely stored on Vkontakte servers and is not available to the program that you distribute:
Stored procedures allow the execution of server-side API code in a manner similar to the execute method, but without transmitting the procedure code over the network.
For additional protection, the stored procedure should, in addition to executing, check whether the user who purchased the license launched it, for this it is enough to execute the stored procedure at the beginning, for example, the following code:
var allowed_users = ",id1,id2,id3,id99999999,";
As an analogue, you can get allowed_users from the wiki page or check it in another way.
Upon expiration of the license from the user, it is simply removed from the allowed_users.
Conclusion
- You can automate the process of editing the list of users when storing the allowed_users list outside a stored procedure
- Simple implementation
- Not suitable for multi-user or demanding project performance
- Slows down the execution of a stored procedure
- Depending on the availability and limitations of Vkontakte
- Vkontakte can be blocked
- Implemented in any service with analogues stored procedures Vkontakte