Today’s lesson we will devote to VLAN settings, that is, we’ll try to do everything that we talked about in previous lessons. Now we will look at 3 questions: creating a VLAN, assigning VLAN ports and viewing the VLAN database.
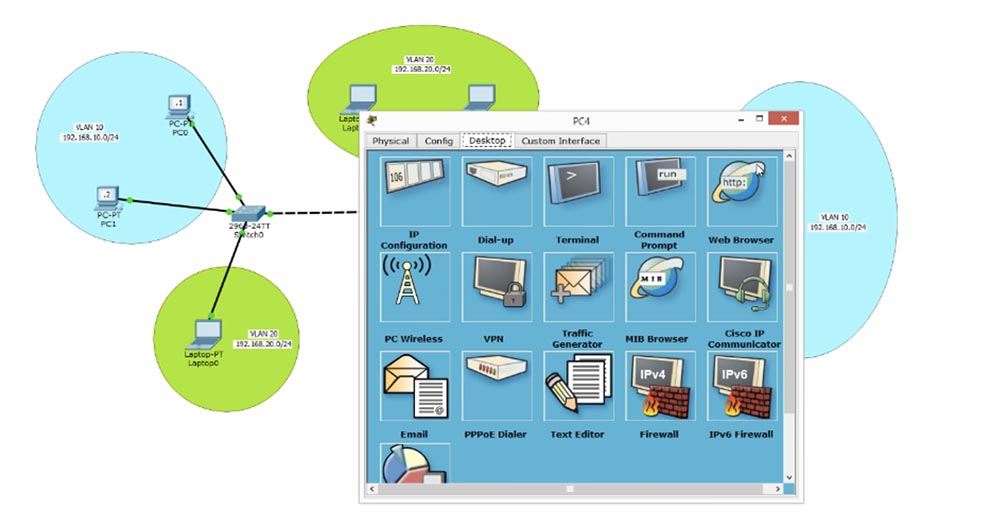
Let's open the Cisco Packer tracer program window with the logical topology of my network drawn by me.
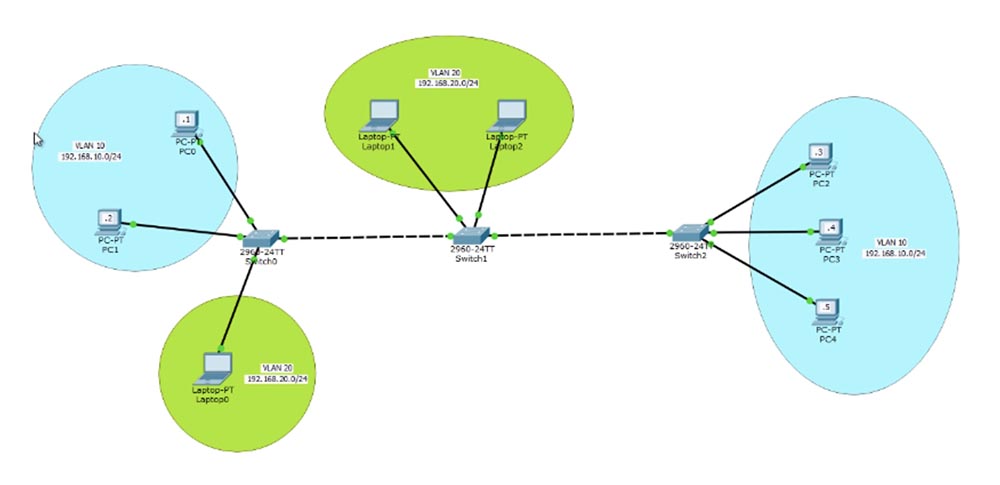
The first switch SW0 is connected to 2 computers PC0 and PC1, connected to a VLAN10 network with a range of IP addresses 192.168.10.0/24. Accordingly, the IP addresses of these computers will be 192.168.10.1 and 192.168.10.2. Usually people identify the VLAN number by the third octet of the IP address, in our case it is 10, however this is not a prerequisite for designating networks, you can assign any VLAN identifier, however this procedure is accepted in large companies because it makes network configuration easier.
Next is the switch SW1, which is connected to the VLAN20 network with the IP address 192.168.20.0/24 with two laptops Laptop1 and Laptop2.
VLAN10 is located on the 1st floor of the company’s office and is a network of sales management. The marketer’s Laptop0 laptop, which belongs to VLAN20, is connected to the same switch SW0. This network extends to the 2nd floor, where other employees are located, and it is connected to the sales department, which can be located in another building or on the 3rd floor of the same office. There are 3 more computers installed - PC2.3 and 4, which are part of the VLAN10 network.
VLAN10, like VLAN20, must provide uninterrupted communication for all employees, regardless of whether they are located on different floors or in different buildings. This is the concept of the network that we will consider today.
Let's set it up and start with PC0. By clicking on the icon, we enter the computer’s network settings and enter the IP address 192.168.10.1 and the subnet mask 255.255.255.0. I do not enter the default gateway address, because it is needed to exit from one local network to another, and in our case we will not deal with OSI level 3 settings, we are only interested in level 2, and we are not going to consider traffic routing to another network.
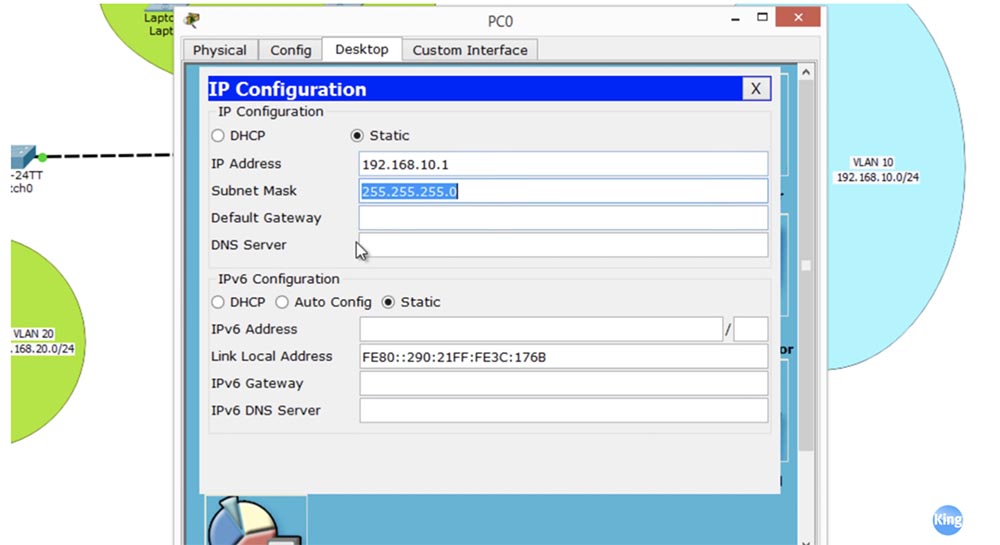
We are going to configure the intranet and only those hosts that are part of it. Then we go to PC2 and do the same as for the first PC. Now check if I can ping PC1 from PC0. As you can see, ping passes and the computer with the IP address 192.168.10.2 confidently returns packets. Thus, we successfully established communication between PC0 and PC1 through a switch.
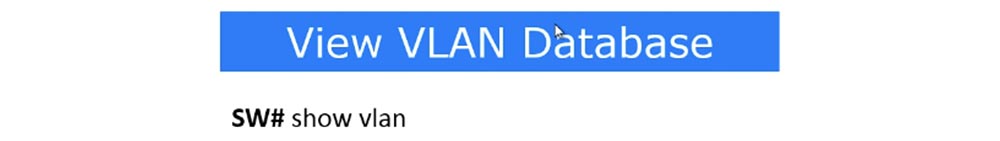
To understand why we succeeded, go to the switch settings and look at the VLAN table.

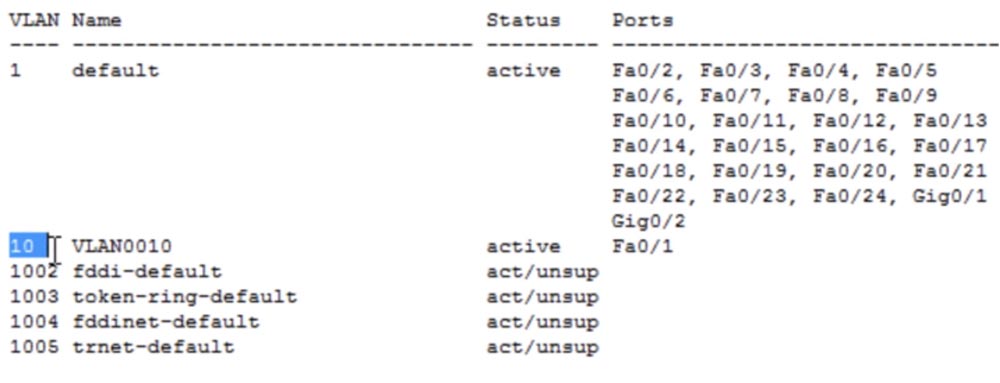
Technically, this switch has 5 VLANs: VLAN1 by default, as well as 1002,1003,1004 and 1005. If you look at the last 4 networks, you can see that they are not supported and are indicated by unsupported. These are virtual networks of old technology - fddi, fddinet, trnet. Currently, they are not used, but according to technical requirements, they are still included in new devices. Thus, in fact, our switch has by default only one virtual network - VLAN1, therefore all ports of any Cisco switch out of the box are configured on this network. These are 24 Fast Ethernet ports and 2 Gigabit Ethernet ports. This greatly facilitates the compatibility of new switches, because by default they are all part of the same VLAN1.
We must reassign the ports that are configured by default to work with VLAN1, to work with VLAN10. Packet Tracer shows that in our case these are Fa0 and Fa0 / 2 ports.
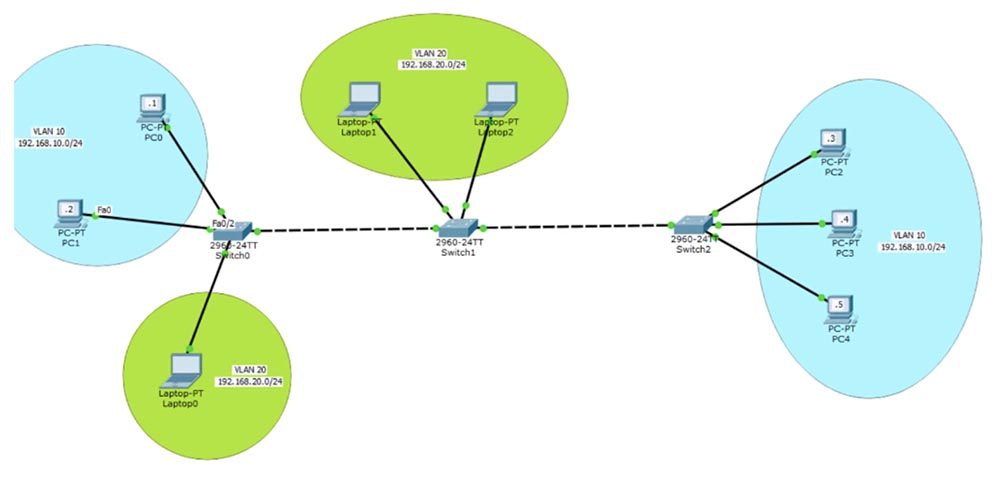
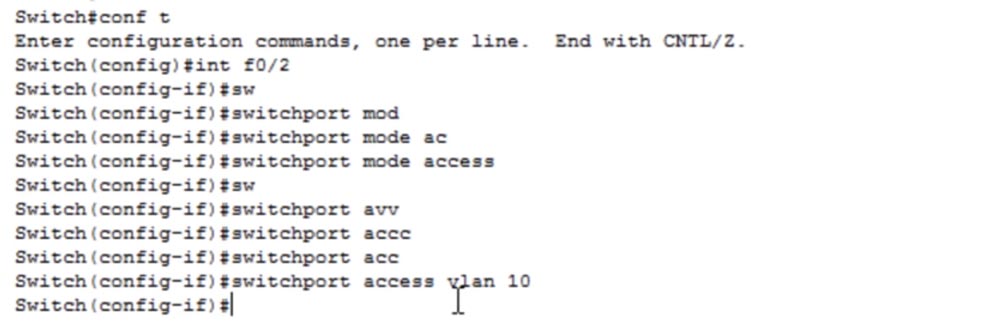
Let's go back to switch SW0 and configure these two ports. To do this, I use the configure terminal command to enter global configuration mode, and enter the configuration command for this interface - int fastEthernet 0/1. I need to set access mode for this port because it is an access port, and I use the switchport mode access command.
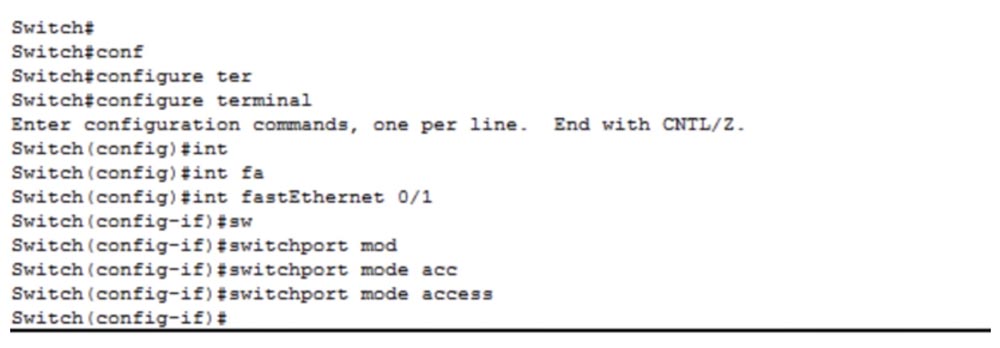
This port is configured as a static access port, but if I connect another switch to it, then using the DTP protocol it will go into dynamic trunk mode. By default, this port belongs to VLAN1, so I need to use the switchport access vlan 10 command. In this case, the system will give us a message that VLAN10 does not exist and needs to be created. If you remember, in the VLAN database we have only one network - VLAN1, and there is no VLAN10 network there. But we requested the switch to provide access to VLAN10, so we received an error message.
Therefore, we need to create VLAN10 and assign this access port to it. After that, if you go into the VLAN database, you can see the newly created VLAN0010, which is in the active state and to which the Fa0 / 1 port belongs.
We did not make any changes to the computer, but simply configured the port of the switch to which it is connected. Now let's try to ping the IP address 192.168.10.2, which we successfully did a few minutes ago. We did not succeed, because the port to which PC0 is connected now belongs to VLAN10, and the port connected to PC1 still belongs to VLAN1, and there is no connection between the two networks. In order to establish communication between these computers, it is necessary to configure both ports to work with VLAN10. I enter global configuration mode again and do the same for switchport f0 / 2.
Let's look at the VLAN table again. Now we see that VLAN10 is configured on the Fa0 / 1 and Fa0 / 2 ports. As you can see, now the ping is successful, because both ports of the SW0 switch, to which the devices are connected, belong to the same network. Let's try changing the name of the network to indicate its purpose. If we want to make any changes to the VLAN, we must go into the configuration of this network.
To do this, I type vlan 10 and you see that the command prompt has changed from Switch (config) # to Switch (config-vlan) #. If you enter a question mark, the system will show us only 3 possible commands: exit, name and no. I can assign a network name using the name command, return the commands to their default state by typing no, or save the changes using the exit command. Therefore, I enter the name SALES and exit commands.
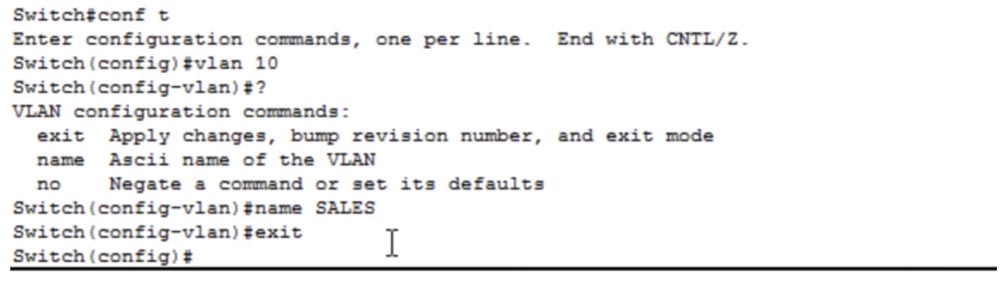
If you look at the VLAN database, you can make sure that our teams are executed and the former VLAN10 is now called SALES - sales department. So, we connected 2 computers of our office to the created network of the sales department. Now you need to create a network for the marketing department. In order to connect Laptop0 laptop to this network, you need to enter its network settings and enter the IP address 192.168.20.1 and subnet mask 255.255.255.0, we do not need a default gateway. Then you need to return to the switch settings, enter the port settings with the int fa0 / 3 command and enter the switchport mode access command. The next command will be switchport access vlan 20.
We again receive a message that such a VLAN does not exist and needs to be created. You can go the other way - I will exit the Switch port configuration (config-if), go to Switch (config) and enter the vlan 20 command, thereby creating a VLAN20 network. That is, you can first create a VLAN20 network, name it MARKETING, save the changes with the exit command, and then configure the port for it.
If you enter the VLAN database with the sh vlan command, you can see the MARKETING network that we created and the corresponding Fa0 / 3 port. I cannot ping computers from this laptop for two reasons: we have different VLANs and our devices belong to different subnets. Since they belong to different VLANs, the switch will discard laptop packets directed to another network because it does not have a port belonging to VLAN20.
As I said, the company is expanding, there is not enough small office on the ground floor, so it places the marketing department on the 2nd floor of the building, installs computers for 2 employees there and wants to communicate with the marketing department on the first floor. To do this, you must first create a trunk between the two switches - port Fa0 / 4 of the first switch and port Fa0 / 1 of the second switch. To do this, I enter the settings of SW0 and enter the commands int f0 / 4 and switchport mode trunk.
There is a switchport trunk encapsulation encapsulation command, but it is not used in new switches, because by default they use 802.1q encapsulation technology. However, older models of Cisco switches used the proprietary ISL protocol, which is no longer used, since now all switches understand the .1Q protocol. Thus, you no longer need to use the switchport trunk enc command.
If you enter the VLAN database now, you can see that the Fa0 / 4 port has disappeared from it. This is because only access ports that are specific to a VLAN are listed in this table. In order to see the trunk ports of the switch, you must use the sh int trunk command.

In the command window, we see that the Fa0 / 4 port is turned on, encapsulates using the 802.1q protocol and belongs to native vlan 1. As we know, if this trunk port accepts untagged traffic, it automatically routes it to the native vlan 1 network. In the next lesson, we'll talk about configuring native vlan, for now just remember how the trunk settings for this device look.
Now I go to the second switch SW1, enter the settings mode int f0 / 1 and repeat the sequence of port settings in the same way as in the previous case. The two ports Fa0 / 2 and Fa0 / 3, to which the laptops of the marketing department are connected, must be configured for access mode and assigned to the VLAN20 network.
In the previous case, we individually configured each switch port, and now I want to show you how to speed up this process using the command line template. You can enter a command to configure the range of interfaces int range f0 / 2-3, as a result of which the command line request will look like Switch (config-if-range) #, and you can enter the same parameter or apply the same command to specified port range, for example, for 20 ports simultaneously.
In the previous example, we used several times the same switchport mode access and switchport access vlan 10 commands for several switch ports. These commands can be entered once if you use a range of ports. I will now enter the switchport mode access and switchport access vlan 20 commands for the selected port range.
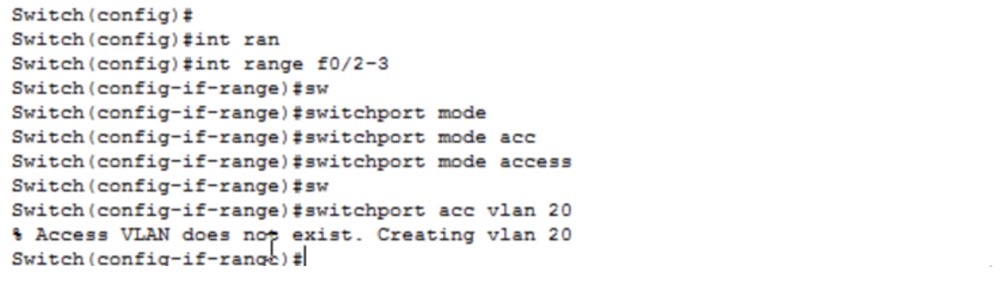
Since VLAN20 does not yet exist, the system will create it automatically. I type exit to save the changes and ask me to show me the VLAN table. As you can see, now the ports Fa0 / 2 and Fa0 / 3 are part of the newly created VLAN20.
Now I will configure the IP addresses of laptops on the second floor of our office: Laptop1 will receive the address 192.168.20.2 and the subnet mask 255.255.255.0, and Laptop2 will receive the IP address 192.168.20.3. Let's check the network performance by pinging the first laptop from the second. As you can see, ping is successful, because both devices are part of the same VLAN and are connected to the same switch.
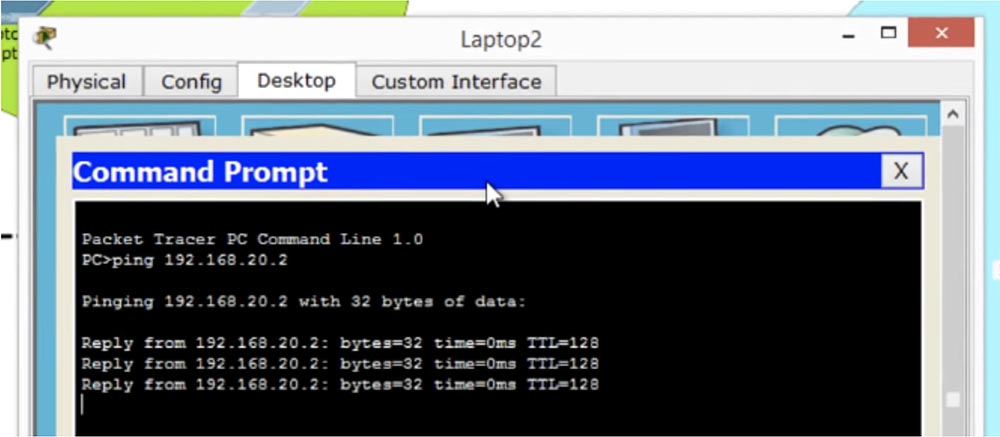
However, the laptops of the marketing department on the first and second floors are connected to different switches, although they are on the same VLAN. Let's check how the connection between them is ensured, for this I am pinging with Laptop2 a laptop on the first floor with the IP address 192.168.20.1. As you can see, everything works without problems, despite the fact that laptops are connected to different switches. The connection is due to the fact that both switches are connected by a trunk.
Can I establish a connection between Laptop2 and PC0? No, I can’t, because they belong to different VLANs. Now let's configure the network of PC2,3,4 computers, for which we first create a trunk between the second switch Fa0 / 4 and the third switch Fa0 / 1.
I go into the settings of SW1 and type config t command, then I call int f0 / 4, then I enter the switchport mode trunk and exit commands. Similarly, I configure the third switch SW2. We created the trunk, and you see that after the settings have taken effect, the color of the ports has changed from orange to green. Now you need to configure the Fa0 / 2.0 / 3.0 / 4 ports to which the sales department computers belonging to the VLAN10 network are connected. To do this, I go into the settings of the SW2 switch, select the port range f0 / 2-4 and apply the switchport mode access and switchport access vlan 10 commands to them. Since there is no VLAN10 network on these ports, it is created automatically by the system. If you look at the VLAN database of this switch, you can see that now the Fa0 / 2.0 / 3.0 / 4 ports belong to the VLAN10 network.
After that, you need to configure the network for each of these 3 computers by entering the IP addresses and subnet masks. PC2 receives the address 192.168.10.3, PC3 receives the address 192.168.10.4, and PC4 receives the IP address 192.168.10.5.
To answer the question whether our network works, we ping the PC0 computer on the first floor from the PC4 computer located on the 3rd floor or in another building. The ping failed, so let's try to figure out why we were unable to do this.
When we tried to ping Laptop0 from Laptop2, everything worked fine, despite the fact that the laptops were connected to different switches. Why now, when our sales department computers are also connected to different switches connected by a trunk, the ping fails? In order to understand the cause of the problem, you need to remember how the switch works.
When we send a packet from PC4 to switch SW2, he sees that the packet is arriving at port Fa0 / 4. The switch checks its database and discovers that the Fa0 / 4 port belongs to the VLAN10 network. After that, the switch tags the frame with the network number, that is, attaches the VLAN10 header to the traffic packet, and sends it over the trunk to the second switch SW1. This switch “reads” the header and sees that the packet is for VLAN10, looks into its VLAN database and, finding that there is no VLAN10 there, discards the packet. Thus, PC2.3 and 4 devices can communicate with each other without problems, but the attempt to establish communication with computers PC0 and PC1 fails, because switch SW1 does not know anything about VLAN10.
We can easily fix this problem by going to the settings of SW1, creating a VLAN10 network using the vlan 10 command and entering its name MARKETING. Let's try pinging again - you see that the first three packets are discarded, and the fourth passes successfully. This is because the switch first checked the IP addresses and determined the MAC address, it took a certain time, so the first three packets were dropped by a timeout. Now the connection is established, because the switch has supplemented its table of MAC addresses and sends packets directly to the desired address.
All I did to fix the problem was go into the settings of the intermediate switch and create a VLAN10 network there. Thus, even if the network is not directly connected to the switch, it should still be aware of all the networks involved in network connections. However, if your network has hundreds of switches, you will not be able to physically go into each setting and manually configure the VLAN identifiers. That's why we use the VTP protocol, the configuration of which will be discussed in the next video tutorial.
So, today we looked at everything we planned: how to create a VLAN, how to assign VLAN ports, and how to view the VLAN database. To create networks, we enter the global configuration mode of the switch and use the vlan <number> command, we can also assign the name of the created network using the name <name> command.
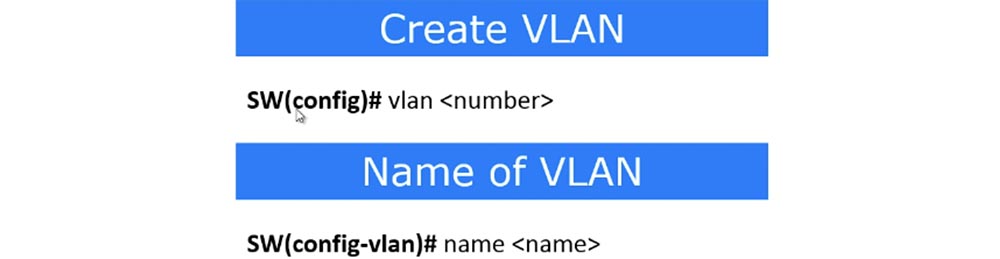
We can also create a VLAN in another way by entering interface mode and using the switchport access vlan <number> command. If there is no network with this number, it will be created automatically by the system. Remember to use the exit command after making changes to the initial settings, otherwise they will not be saved in the VLAN database. Next, you can assign ports to specific VLANs using the appropriate commands.

The switchport mode access command puts the interface into static access-port mode, after which the corresponding VLAN number is assigned to the port with the switchport access vlan <number> command. To view the VLAN database, use the show vlan command, which must be entered in EXEC user mode. To view the list of trunk ports, use the show int trunk command.
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending it to your friends, a
30% discount for Habr users on a unique analogue of entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to divide the server? (options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have
2 x Intel TetraDeca-Core Xeon 2x E5-2697v3 2.6GHz 14C 64GB DDR4 4x960GB SSD 1Gbps 100 TV from $ 199 in the Netherlands! Dell R420 - 2x E5-2430 2.2Ghz 6C 128GB DDR3 2x960GB SSD 1Gbps 100TB - from $ 99! Read about
How to Build Infrastructure Bldg. class c using Dell R730xd E5-2650 v4 servers costing 9,000 euros for a penny?