Introduction
Hello again.
This time the article will not raise “serious” questions.
This will be a story about how, without knowing the programming, but being quite savvy and attentive, you can find a serious vulnerability that, for example, will allow you to write off all money from an account with only a username and password (read, bypass two-factor authentication or same confirmation by SMS).
At the moment, Qiwi has already patched it safely, so I will try to reinforce the explanations with modern screenshots, sometimes explaining how it looked 2.5 years ago.
Now to the point
Suppose you have a username: the password to someone else's Qiwi wallet.
Let's say there is 100k rubles.
And you sooooo want to take possession of them.
But you can’t just write off money - you need confirmation by SMS.
But we are smart, this will not stop us.
Step 1. Log in to your account and create a virtual card there.We see such a picture
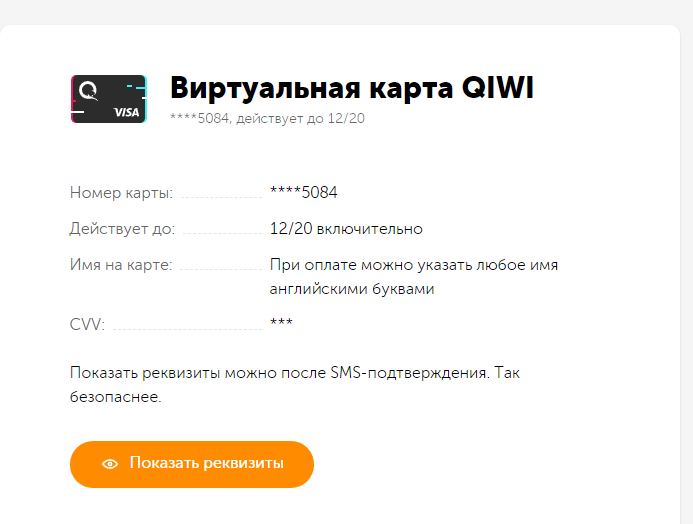
It looks like we have very little information. Only the last 4 digits of the card and the duration of the card.
But
before there were 6 (!) Last digits of the card . That is, another 10 digits were unknown.
And we need all the numbers on the card. Where to get more? Very simple.
All cards have a BIN - the first 6 digits of cards of a certain bank of the same type should be the same.
Step 2. We climb into the browser and google “Qiwi BIN”Immediately we find out that the bin is 489049.
And now we already have 12 digits! Only 4 left!
But here comes the difficulty.
These 4 digits do not flicker anywhere and, it would seem, there is nowhere to get them.
But, of course, if you try hard, you can find :)
Step 3. Find the last 4 digits missingTo do this, we need to have an account in Qiwi with 1000r and know what the
Moon Algorithm is .
Let's go in order.
If you open any transaction in Qiwi, then it shows the payment date and receipt number.
Maybe some have already guessed why we need 1k in the account.
Yes, we will substitute the numbers in order instead of those unknown 4 digits that remain unknown and send them to the card numbers in rubles!
And in one of the operations we will receive an incoming 1p to the account where the treasured 100k rubles lie.
It remains only to compare the time of sending money.
Previously, it was possible to match operation numbers, but now they have hidden it. And they did it right.
And now the most attentive will say that in fact 4 digits are 10k operations, not 1k. So you need 10k rubles and a lot of time to find the right 4 digits.
And this is not entirely true. I present to you the
Moon Algorithm!The Luhn algorithm is an algorithm for calculating the check digit of a plastic card number in accordance with ISO / IEC 7812. It is not a cryptographic tool, but is primarily intended to detect errors caused by inadvertent data corruption (for example, when manually entering a number cards, when receiving data on the social security number by phone). It allows only with a certain degree of reliability to judge the absence of errors in the block of numbers, but does not allow finding and correcting the discovered inaccuracy.
If it’s very interesting - google, and I will tell you briefly about the algorithm and how it will help us.
This algorithm allows you to confirm whether the card number is valid. That is, having driven our 10k options through this algorithm, you can leave only the numbers of potentially existing cards. Guess how many there will be?
Right, exactly 1k.
Of course, all this seems very handy to do manually, but what prevents a simple script from generating these very 1k options?
Here are some Wikipedia implementation examples:
Moon Algorithm Example on JSfunction luhnAlgorithm(digits) { let sum = 0; for (let i = 0; i < digits.length; i++) { let cardNum = parseInt(digits[i]); if ((digits.length - i) % 2 === 0) { cardNum = cardNum * 2; if (cardNum > 9) { cardNum = cardNum - 9; } } sum += cardNum; } return sum % 10 === 0;}
Example Moon Algorithm in PHP function luhnAlgorithm($digit) { $number = strrev(preg_replace('/[^\d]/', '', $digit)); $sum = 0; for ($i = 0, $j = strlen($number); $i < $j; $i++) { if (($i % 2) == 0) { $val = $number[$i]; } else { $val = $number[$i] * 2; if ($val > 9) { $val -= 9; } } $sum += $val; } return (($sum % 10) === 0); }
Now we need to sort through these 1k options using the method I described above.
And voila - we got the last 4 digits.
Now we have the full card code and its expiration date.Of course, we do not have CVV code (the one that is written on the reverse side), but in some places it is not needed.
For example Amazon!
Yes, we go to Amazon and order anything with the help of newly made data.
For example, Steam codes for money or something like that. In general, there is something electronic to quickly sell on the Internet. We will lose a little in money, but not more than 20%, most likely.
That's all! Got + 79k profit!
Do not forget that this is no longer working!
But if you find something similar - tell Qiwi, they will (hopefully) fix it.
I laid it out to show that you can find cool things and security holes without even being able to program. And for general development.
Good luck to all :)